This document provides details on the installation and configuration of the SSO feature in System Management Hub.
SSO manages centrally user authentication. Once the user is authenticated, the application passes a token and / or an artifact that is used by the IAF server.
The architecture of IAF defines a central service (the IAF service). It creates the IAF token that contains all the information about the authenticated user and the IAF artifact that is a short index to the information about the user. In System Management Hub, the SSX configuration provides a GUI for setting the IAF service.
The information is organized under the following headings:
After successful authentication in CTP on the IAF server, each plug-in of the Pluggable UI is provided with a user name and an IAF artifact instead of a password. These credentials are used for authentication on the Client/Server Layer.
The diagram below illustrates the SSO workflow in System Management Hub:
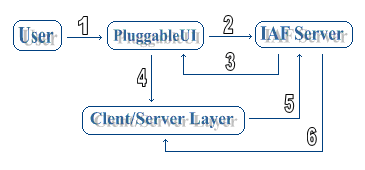
Following is an explanation of the different steps of the SSO authentication.
![]() To authenticate on the system using SSO
To authenticate on the system using SSO
A user tries to authenticate on the system using the authentication interface provided by the Pluggable UI. (--1-->)
The Pluggable UI sends a request for a token to the IAF server. (--2-->)
The IAF server sends back the token to the Pluggable UI. (--3-->)
The token is sent to the Client/Server Layer of System Management Hub. (--4-->)
The Client/Server Layer sends a request for token validation to the IAF server. (--5-->)
The IAF server validates the token and returns it to the Client/Server Layer. (--6-->)
The IAF service is contacted by multiple clients in order to do the following:
Authenticate a user
Create a unique and fraud-resistant token
Create an artifact for the existing token
Validate tokens or artifacts
Pass information about the token and the authenticated user to the owner of the token
The installation of the IAF service comes with the product installation of a Software AG application. The service is disabled by default on Windows and UNIX.
![]() To Enable the IAF Service on Windows and UNIX
To Enable the IAF Service on Windows and UNIX
On Windows, right-click My Computer and select Manage -> Services and Application -> Software AG Integrated Authentication Framework Service.
On UNIX, run /etc/init.d/sag<n>iafd
start/stop.
![]() To use the IAF service
To use the IAF service
Pass the URL of the IAF server to the application.
Following are the custom parameters for IAF configuration in the SSX login module:
| Parameter | Description | Mandatory |
|---|---|---|
| IAFserverHost |
Host of the IAF server. Specify the host name (plus SSL port) of the IAF server. To do this, either use For example,
|
Yes |
| IAFCertLocation |
Location of the IAF certificate. For example, |
No |
| serverHost |
The host of the server. The combination of Specify the For example,
|
Yes |
| localCodePage |
Local code page for IAF communication. This is required because the transport protocol encoding is UTF-8. On IBM mainframes, the default code page is "IBM_037", elsewhere it is "ISO8859-1". |
No |
| homeDir |
Locates the broker stub module and the crypto library. SSX looks for specific libraries. The homeDir paramter specifies the path to those libraries and loads them dynamically. Following is a list of the libraries for the different operating systems:
For example (Windows): homeDir="C:\<Software AG_directory>\webMethods\<DIR_DLL_Libraries>" |
No |
To use SSO in System Management Hub, you must configure SSX to use the IAF service for authentication.
The configuration panel for the IAF service is under the menu of the :
If the SSX configuration is disabled, you must use the option (that appears in the place of ) to activate it.
Following is a screen capture of the default IAF configuration:
![]() To set the authentication type to IAF
To set the authentication type to IAF
Right-click the menu.
Select .
In the right panel of the screen, set the authentication type to IAF.
Click to go to the text field for entering the IAF host. System Management Hub offers a tooltip for entering the correct format for the IAF host. Point to the text field to see it:
Click to complete the configuration.