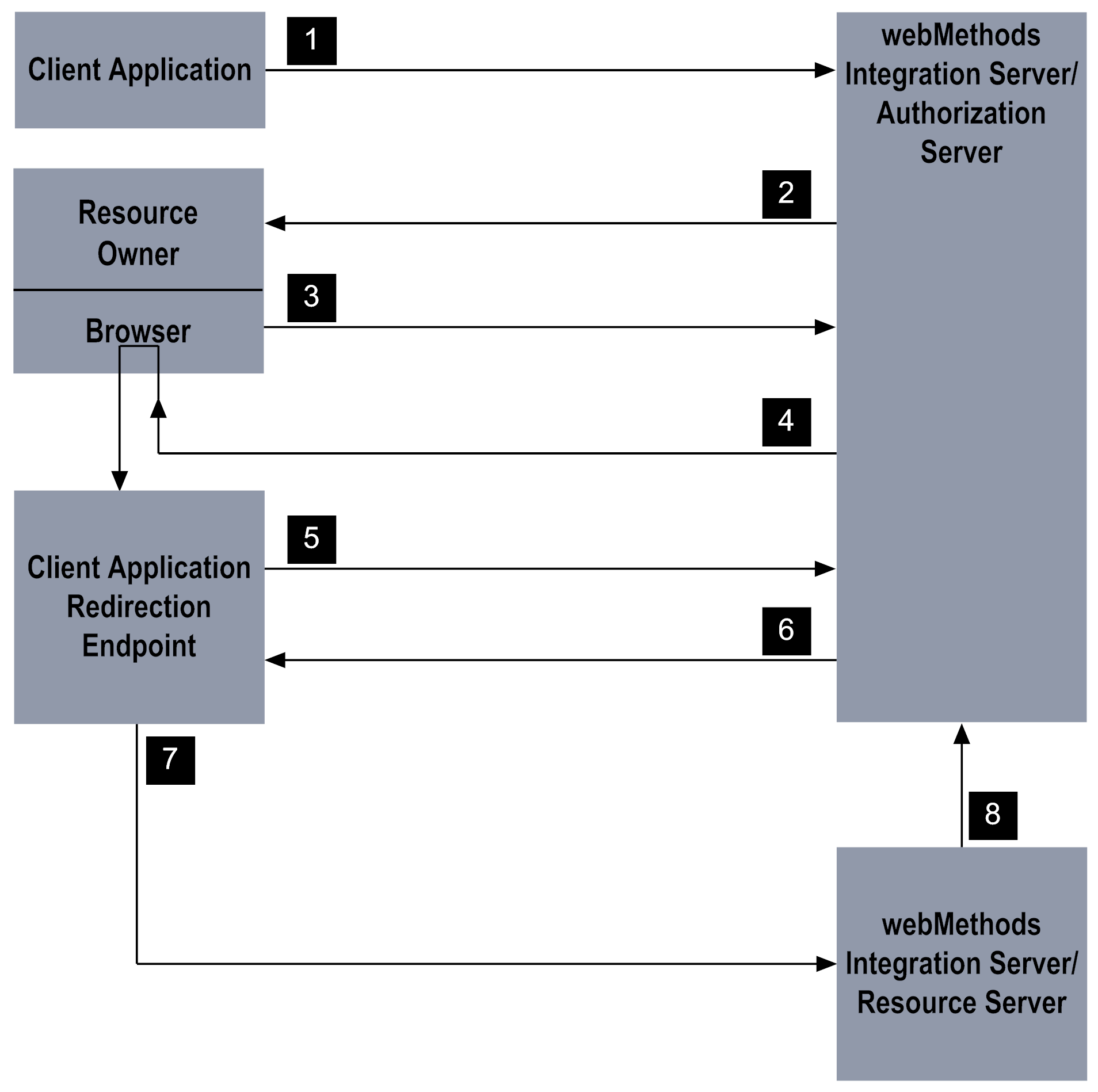
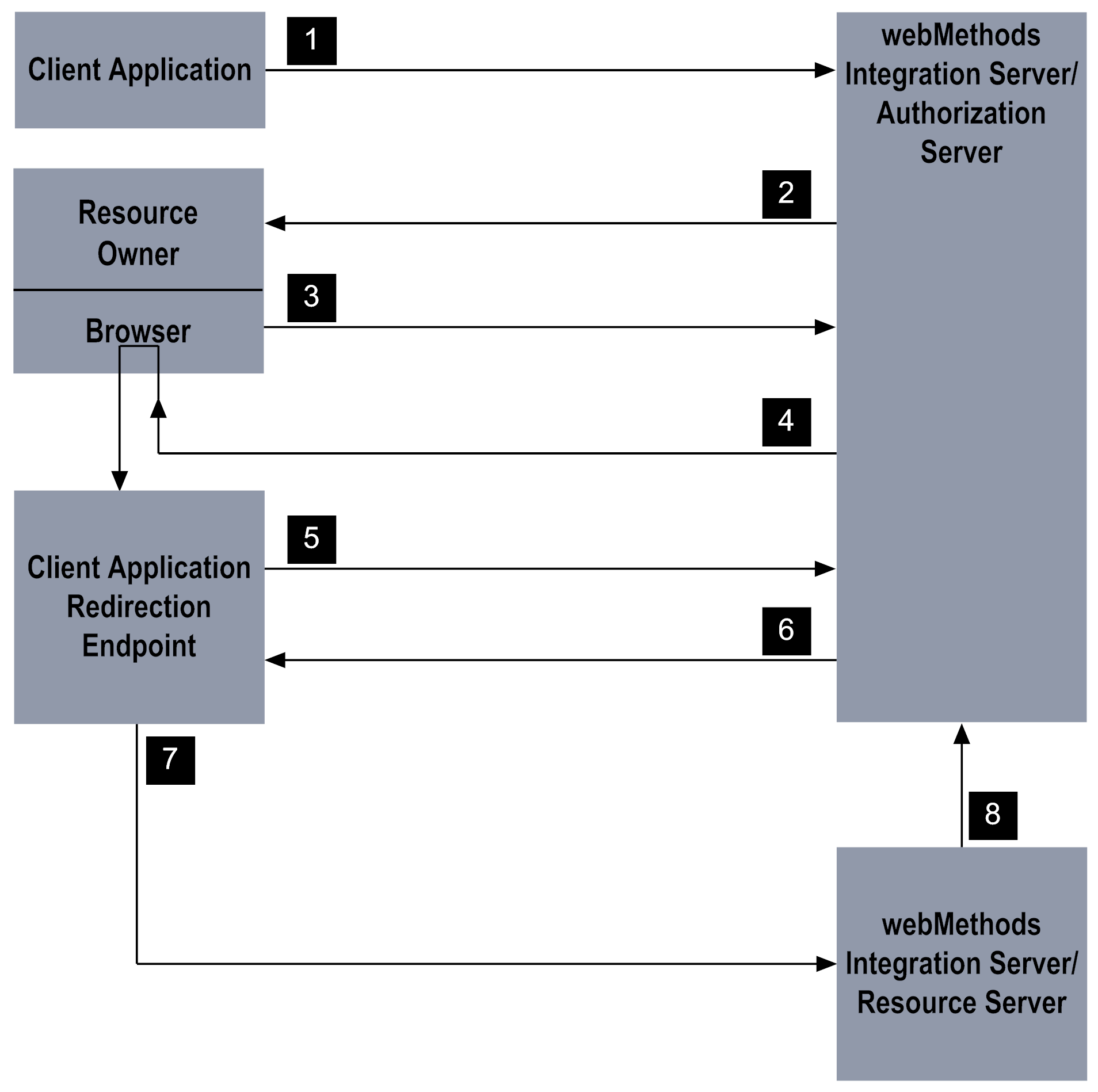
Stage | Description |
1 | The client application initiates the process by calling the pub.oauth:authorize service to request access to the resource owner’s data. |
2 | The pub.oauth:authorize service validates the request. If valid, the service responds with an HTML page that informs the resource owner that the client application is requesting access within a specified scope. The resource owner uses the HTML page to approve or deny the request. |
3 | When the resource owner approves the request, the approval page invokes an internal service on Integration Server. If the resource owner denies the request, an error is returned. |
4 | Integration Server generates an authorization code for the client application. The server uses HTTP redirection to instruct the resource owner's browser to transmit the authorization code to the redirection URI provided by the client application. |
5 | The service at the client application’s redirection URI passes the authorization code to the pub.oauth:getAccessToken service on Integration Server to exchange the authorization code for an access token. |
6 | Integration Server issues an access token to the client application. If set to do so, the authorization server also issues a refresh token to the client. |
7 | The client application uses the access token to execute a service on the resource server. |
8 | The resource server checks with the authorization server to make sure the requested service is within the scope for which the access token was issued and whether the client is authorized to access the folders and services in the scope. |