Configuring Single Sign-On for ActiveTransfer Web Client
ActiveTransfer supports Single Sign-On (SSO) through Security Assertion Markup Language (SAML) 2.0, an XML-based framework for the exchange of security information. You can use SAML to access ActiveTransfer web client through SSO. SSO is supported only for HTTPS protocol.
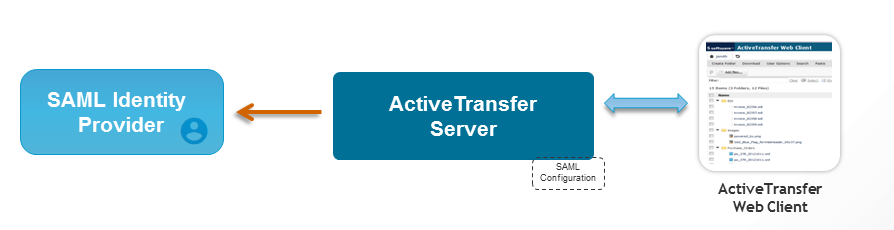
ActiveTransfer serves as the service provider (SP) and communicates between a third-party identity provider (IDP) such as, ADFS, Okta, and so on, to access the target application, ActiveTransfer web client. You can configure ActiveTransfer for exchanging authentication data between the third-party identity provider and ActiveTransfer service provider. The third-party identity provider is the SAML authority and ActiveTransfer is the SAML consumer.
Who are involved?
 ActiveTransfer
ActiveTransfer administrator, who performs SSO configurations in
ActiveTransfer.

Identity provider administrator, who creates an identity provider account and manages the SSO configurations for
ActiveTransfer.
 ActiveTransfer
ActiveTransfer web client users, who use the
ActiveTransfer web client to perform file transfers.
Visual Model
Preconditions

Keys for generating signed and encrypted SAML requests

IP Metadata XML

User with SSO credentials

User associated with
ActiveTransfer web client through VFS

Redirection URI, which is the URL generated or shared by the identity provider to access the
ActiveTransfer web client

Third party SAML provider such as ADFS, Keycloak, OKTA and so on
Basic Flow
To enable SSO for
ActiveTransfer Web Client, see
Configuring Additional Settings for a Listener.
How Does SSO Work When The User Accesses ActiveTransfer Web Client?
1. For the first-time login, the user types the ActiveTransfer web client URL (for example, https://localhost:234) in a web browser.
The first-time logins are preauthenticated by the browser and redirected to the identity provider for login. The SAML identity window appears.
2. The user types the user name and password.
3. An SSO token is sent through the HTTPS port to the identity provider and results in one of the following:

The SAML configuration is authenticated successfully.
ActiveTransfer web client is displayed. The user can switch between the applications without having to log in again.

The SAML configuration is not authenticated successfully and the user authentication fails. In the next login, the user can do one of the following:

Bypass SSO login to the HTTPS port by appending
nosso at the end of the URL. For example,
https://servername:port/nosso.

Login using the user name and password.