This section covers the following topics:
With Natural Security, you can control the use of various types of objects used by:
The term external objects used in the Natural Security documentation comprises all the object types listed below.
The following are Predict object types (they are described in the Predict documentation):
documentation objects (*PRD-Docu-Object) (PO)
external objects (*PRD-Ext-Object) (PE)
functions (*PRD-Function) (PF)
3GL libraries (*PRD-3GL-Library) (PL)
The two-letter codes in parentheses are the corresponding object-type codes as used by some Natural Security functions.
| Warning: For documentation objects of types "base application" and "compound application" (SY-B and SY-O), it is strongly recommended that instead of Natural Security's subsystem for external objects you use the application maintenance subsystem; see the section Protecting Natural Development Server Applications |
The following types of objects are used by various other products (they are described in the corresponding product documentation):
batch jobs (JB)
datasets (DS)
nodes (ND)
operations (OP)
printers (PR)
volume serials (VS)
VTAM applications (VT)
The two-letter codes in parentheses are the corresponding object-type codes as used by some Natural Security functions.
IDs are used by Natural Security to identify external objects and their security profiles. The ID of an external object must be unique amongst all IDs of objects of the same type defined to Natural Security.
The length of the IDs and other naming conventions that may apply to external objects differ from object type to object type; please refer to the respective product documentation for information.
For the ID of an external object, you can use asterisk notation: if you create a security profile for an external object and choose as ID a character string followed by an asterisk (*), the security profile will apply to all objects of that type whose IDs begin with that character string. For single objects (or ranges of objects) within such a range you may still define individual security profiles.
For example, you can create a security profile for a batch job with ID "ADAX", which will apply to batch job ADAX; moreover, you can create a security profile for a batch job with ID "ADA*", which will apply to all other batch jobs whose IDs begin with "ADA"; further, you can create a security profile for a batch job with ID "A*", which will apply to all other batch jobs whose IDs begin with "A"; and, you can also create a security profile for a batch job with ID "*", which will apply to all other batch jobs for which no individual security profiles are defined.
The following type of screen is the "basic" security profile screen for an external object, which is displayed when you invoke one of the functions Add, Copy, Modify, Display for an external object's security profile:
11:31:46 *** NATURAL SECURITY *** 2012-10-31
- Modify Dataset -
Modified .. 2012-09-12 by SAG
Dataset ........... XYZ.SYS.SOURCE
------ Default Access -------
N I Info
N R Read
N A Alter
N D Delete
Additional Options ... N
Enter-PF13--PF14--PF15--PF16--PF17--PF18--PF19--PF20--PF21--PF22--PF23--PF24---
Refr Menu
|
This screen varies slightly from object type to object type.
The individual items you may define as part of an external object's security profile are explained below.
In this column, you can allow/disallow general access methods for the external object. The possible access methods differ from object type to object type, as shown below:
| Access to Predict Documentation Objects, External Objects and 3GL Libraries: | |
|---|---|
| R | Read |
| A | Add |
| M | Modify |
| D | Delete |
| Access to Predict Functions: | |
| E | Execute |
| Access to Batch Jobs: | |
| I | Display |
| S | Submit |
| A | Alter |
| D | Delete |
| Access to Datasets: | |
| I | Info |
| R | Read |
| A | Alter |
| D | Delete |
| Access to Nodes, Printers, VTAM Applications: | |
| U | Use |
| Access to Operations: | |
| P | Passive |
| A | Active |
| Access to Volume Serials: | |
| I | Info |
| C | Allocate |
| A | Alter |
| D | Delete |
The individual access methods are the same as those described in the corresponding product documentation.
Mark with "Y" the access methods that are to be allowed; mark with "N" the access methods that are not to be allowed.
The access methods allowed/disallowed here will apply to all users for which no special access is defined via a link (for information on links, see Linking Users to External Objects below).
If you mark the field Additional Options on the basic security profile screen with "Y", a window will be displayed from which you can select the following options:
Maintenance Information
Security Notes
Owners
The options for which something has already been specified or defined are marked with a plus sign (+).
You can select one or more items from the window by marking them with any character. For each item selected, an additional window will be displayed:
| Additional Option | Explanation |
|---|---|
| Maintenance Information (display only) | The following information is displayed:
|
| Security Notes | You may enter your notes on the security profile. |
| Owners | You may enter up to eight IDs of administrators. Only the
administrators specified here will be allowed to maintain the security profile.
If no owner is specified, any user of type "Administrator" may maintain the security profile. For each owner, the number of co-owners whose countersignatures will be required for maintenance permission may optionally be specified in the field after the ID. For an explanation of owners and co-owners, see the section Countersignatures. |
This section describes the functions used to create and maintain security profiles for external objects. It covers the following topics:
![]() To invoke external object maintenance:
To invoke external object maintenance:
On the Main Menu, select Maintenance.
A window will be displayed.
In the window, mark one type of external object with a character or with the cursor.
The Maintenance selection list for the selected object type will be displayed.
From this selection list, you invoke all maintenance functions as described below.
The Add External Object function is used to define external objects to Natural Security, that is, create security profiles for them.
![]() To add a new external object:
To add a new external object:
In the command line of the external object
Maintenance selection list, enter the command
ADD.
A window will be displayed.
In this window, enter an ID for the object.
The Add screen for the specified object type will be displayed.
On this screen, you may define a security profile for the external object.
The individual items you may define on this screen and any additional windows that may be part of an external object's security profile are described under Components of an External Object's Security Profile above.
When you add a new external object, the owners specified in your own user security profile are automatically copied into the external object's security profile.
When you invoke Maintenance for an external object, a list of all external objects of this type for which a security profile exists will be displayed.
If you do not wish to get a list of all existing external objects but would like only certain external objects to be listed, you may use the Start Value option as described in the section Finding Your Way In Natural Security.
On the Main Menu, select Maintenance. A window will be displayed.
In the window, mark one type of external object with a character or with the cursor (and, if desired, enter a start value). The selection list for the selected object type will be displayed; for example:
13:11:23 *** NATURAL SECURITY *** 2012-10-31
- Dataset Maintenance -
Co Dataset Message
__ ______________________________________________________ _____________________
__ XYZ.S
__ XYZ.SYS
Command ===>
Enter-PF1---PF2---PF3---PF4---PF5---PF6---PF7---PF8---PF9---PF10--PF11--PF12---
Help Exit Flip - + Canc
|
The list can be scrolled as described in the section Finding Your Way In Natural Security.
The following maintenance functions are available for external objects (possible code abbreviations are underlined):
| Code | Function |
|---|---|
CO |
Copy |
MO |
Modify |
RE
|
Rename |
DE
|
Delete |
DI |
Display |
LU
|
Link user |
The individual functions are described below.
To invoke a specific function for an external object, mark the object with the appropriate function code in column Co.
You may select various objects for various functions at the same time; that is, you can mark several objects on the screen with a function code. For each object marked, the appropriate processing screen will be displayed. You may then perform for one object after another the selected functions.
The Copy function is used to define a new external object to Natural Security by creating a security profile which is identical to an already existing external object's security profile.
All components of the existing security profile will be copied into the new security profile - except the owners (these will be copied from your own user security profile into the new security profile).
Any links that exist to the existing external object will not be copied.
On the Maintenance selection list, mark the
external object whose security profile you wish to duplicate with function code
CO.
A window will be displayed. In the window, enter the ID of the new external object.
The Copy screen for the external object will be displayed showing the new security profile.
This screen and any additional windows that may be part of an external object's security profile as well as the individual items you may define or modify are described under Components of an External Object's Security Profile above.
The Modify function is used to change an existing external object's security profile.
On the Maintenance selection list, you mark the
external object whose security profile you wish to change with function code
MO. The Modify screen for the external object
will be displayed.
This screen and any additional windows that may be part of an external object's security profile as well as the individual items you may define or modify are described under Components of an External Object's Security Profile above.
The Rename function allows you to change the ID of an existing external object's security profile.
On the Maintenance selection list, you mark the
external object whose ID you wish to change with function code RE.
A window will be displayed in which you can enter a new ID for the external
object.
The Delete function is used to delete an existing external object's security profile.
On the Maintenance selection list, you mark the
external object you wish to delete with function code DE. A window
will be displayed.
If you have invoked the Delete function and should then decide against deleting the given external object's security profile, leave the Delete window by pressing ENTER without having typed in anything.
If you wish to delete the given external object's security profile, enter the object's ID in the window to confirm the deletion.
When you delete an external object, all existing links to the external object will also be deleted.
If you mark more than one external object with DE, a
window will be displayed in which you are asked whether you wish to confirm the
deletion of each external object's security profile with entering the object's
ID, or whether all external objects selected for deletion are to be deleted
without this individual confirmation. Be careful not to delete an external
object accidentally.
The Display function is used to display an existing external object's security profile.
On the Maintenance selection list, you mark the
external object whose security profile you wish to view with function code
DI. The Display screen for the external
object will be displayed.
The items displayed on this screen and any additional windows that may be part of a external object's security profile are explained under Components of an External Object's Security Profile above.
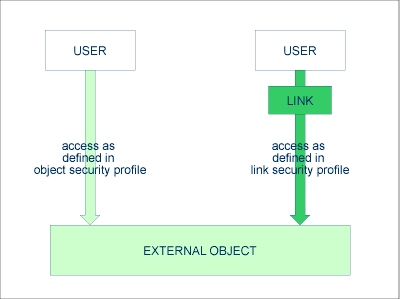
The access methods allowed/disallowed in an external object's security profile apply to all users who are not linked to the external object.
If you wish to allow an individual user more or less access methods, you can link the user to the external object and in the link's security profile define which access methods are to be available for this particular user. This means that by using links you may define for different users different access rights to the same external object.
Only users of types "Administrator", "Person" and "Group" can be linked to an external object. "Administrator"s and "Person"s can be linked to an external object either directly or via a "Group". Users of types "Member" and "Terminal" can be linked to an external object only via a "Group"; that is, they must be assigned to a "Group", and the "Group" be linked to the external object.
Two functions are available to establish and maintain links between users and external objects:
To link one user to various external objects, use the User Maintenance function "Link user to external objects".
To link various users to one external object, use the External Object Maintenance function "Link users to external object".
Both functions are described below.
The function "Link user to external objects" is used to link one user to one or more external objects.
On the User Maintenance selection list, you mark
the user you wish to link with function code LO.
A window will be displayed, in which you mark with the cursor or with a character the type of external object to which you wish to link the user. In addition, the window provides the following options:
Start value - Here you can enter a start value (as described in the section Finding Your Way in Natural Security) for the list of objects to be displayed.
Selection criterion - N = none: all objects will be listed; L = linked: only objects to which the user is already linked will be listed; U = unlinked: only objects to which the user is not yet linked will be listed.
Then, the Link User To External Objects selection list will be displayed, showing the list of objects. For example:
16:04:48 *** NATURAL SECURITY *** 2012-10-31
- Link User to Dataset -
User ID .... AD User Name .... ARTHUR DENT
Access
Co Dataset IRAD Message
__ _____________________________________________ ________ _____________________
__ XYZ.S I_______
__ XYZ.SYS I_A_____
Enter-PF1---PF2---PF3---PF4---PF5---PF6---PF7---PF8---PF9---PF10--PF11--PF12---
Help Exit Flip - + Canc
Command ===> _________________________________________________________________
|
The list can be scrolled as described in the section Finding Your Way In Natural Security.
On the list, you mark the external objects to which you wish to link the user.
In the Co column, you may mark each object with one of the following function codes (possible code abbreviations are underlined):
| Code | Function |
|---|---|
LK
|
Link - The user may use the external object with a special security profile to be defined for the link; the link profile will take precedence over the external object's profile (see below). |
CL
|
Cancel - An existing link will be cancelled. |
DI |
Display Object - The object's security profile will be displayed. |
DL
|
Display Link - The link security profile will be displayed. |
You can mark one or more objects on the screen with a function code. For each object marked, the selected functions will then be executed one after another. When processing is completed, a message will be displayed stating the link situation now in effect between the user and each object.
If you mark an external object with LK, you may define
the security profile for this link on the screen which will be displayed. The
default settings which will appear in the link security profile are taken from
the security profile of the external object.
The items you may define as part of a link security profile correspond with the items you may define as part of an external object's security profile (see Components of an External Object's Security Profile above).
Instead of allowing/disallowing the access methods in the link security profile, you can also enter/delete the corresponding letter in the appropriate position in the Access column of the Link User To External Objects selection list.
Moreover, you have the option to set Activation Dates in the link security profile; these are in analogy to the Activation Dates in a user security profile (as explained under Components of a User Profile in the section User Maintenance).
To modify an existing link security profile, you mark the respective
external object with LK again on the Link User To
External Objects screen to invoke the link security profile
screen.
The function "Link users to external object" is used to link one or more users to one external object.
On the Maintenance selection list of an external
object, you mark the object to which you wish to link users with code
LU.
A window will be displayed, providing the following options:
Start value - Here you can enter a start value (as described in the section Finding Your Way in Natural Security) for the list of users to be displayed.
Selection criterion - N = none: all users will be listed; L = linked: only users already linked to the object will be listed; U = unlinked: only users not yet linked to the object will be listed.
Then, the Link Users To External Object selection list will be displayed. For example:
13:21:12 *** NATURAL SECURITY *** 2012-10-31
- Link Users to Dataset -
Dataset ........... ABC.S
Default Access .... I
Access
Co User ID User Name T IRAD Message
__ ________ ________________________________ _ ________ _____________________
__ AD ARTHUR DENT A I_A_____
__ ADMIN1 BUNGALOW BILL A I_AD____
__ ADMIN2 MARIA ALVAREZ P I_______
__ ADMIN3 SARA SANDOVAL A I_______
__ ADMIN4 ALOYSIUS PENDERGAST A IRA_____
__ ADMIN5 JACK SPARROW A __AD____
__ ADSON BRIAN OF NAZARETH A I_______
__ AGROUP CUALQIER GRUPO G I__D____
__ HC HAGBARD CELINE P I_______
__ KG KARL GLOGAUER P IR______
__ MW MIA WALLACE A I_______
__ NH NATHANIEL HAWKEYE A ___D____
Command ===> _________________________________________________________________
Enter-PF1---PF2---PF3---PF4---PF5---PF6---PF7---PF8---PF9---PF10--PF11--PF12---
Help Exit Flip - + Canc
|
The list includes all users of types "Group", "Administrator" and "Person".
The list can be scrolled as described in the section Finding Your Way In Natural Security.
On the list, you may mark the users you wish to be linked to the external object.
In the Co column, you may mark each user with one of the following function codes (possible code abbreviations are underlined):
| Code | Function |
|---|---|
LK
|
Link - The user may use the external object with a special security profile to be defined for the link; the link profile will take precedence over the external object's profile (see below). |
CL
|
Cancel - An existing link will be cancelled. |
DI |
Display User - The user security profile will be displayed. |
DL
|
Display Link - The link security profile will be displayed. |
You can mark one or more users on the screen with a function code. For each user marked, the selected functions will then be executed one after another. When processing is completed, a message will be displayed stating the link situation now in effect between the user and each object.
If you mark a user with LK, you may define the security
profile for this link on the screen which will be displayed. The default
settings which will appear in the link security profile are taken from the
security profile of the external object.
The items you may define as part of a link security profile correspond with the items you may define as part of an external object's security profile (see Components of an External Object's Security Profile above).
Instead of allowing/disallowing the access methods in the link security profile, you can also enter/delete the corresponding letter in the appropriate position in the Access column of the Link Users To External Object selection list.
Moreover, you have the option to set Activation Dates in the link security profile; these are in analogy to the Activation Dates in a user security profile (as explained under Components of a User Profile in the section User Maintenance).
To modify an existing link security profile, you mark the respective user/object with "LK" again on the Link Users To External Object screen to invoke the link security profile screen.