As explained in the section Natural Security On Different Platforms, the protection of DDMs with Natural Security is different on mainframe computers from that on other platforms. This section describes how to control the use of DDMs (files) on mainframe computers. The control of DDMs on other platforms is described in the section Protecting DDMs On UNIX And Windows.
This section covers the following topics:
In Natural Security on mainframe computers, DDMs are called "files". To define DDMs to Natural Security, you use the File Maintenance functions of Natural Security.
A DDM must have been generated (in Predict, or with the Natural utility SYSDDM), before it can be defined as a file to Natural Security.
The following type of screen is the "basic" file security profile screen, which appears when you invoke one of the functions Add, Copy, Modify, Display for a file security profile:
10:25:36 *** Natural Security *** 2007-09-01
- Modify File -
File ID .. EMPLOYEES Modified .. 2007-05-13 by SAG
DBID ..... 10
FNR ...... 16
Status ... PUBL (PUBL, ACCE, PRIV)
-- DDM Modifiers --
________ _
________ _
________ _
________ _
________ _
________ _
________ _
________ _
Additional Options ... N
Enter-PF1---PF2---PF3---PF4---PF5---PF6---PF7---PF8---PF9---PF10--PF11--PF12---
Help PrevM Exit AddOp Flip Canc
|
The individual items you may define as part of a file security profile are explained below.
| Field | Explanation | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| File ID (display only) | The ID by which the file is defined to Natural Security and for
which a DDM exists in the Natural system file.
The file ID by which a file is defined to Natural Security must be identical to that of the DDM. A file ID may be up to 32 characters long and must be unique among all file IDs defined to Natural Security. |
||||||||||
| DBID / FNR (display only) | The database ID and file number of the database file referenced by the DDM. These values are taken from the DDM and written into the security profile. | ||||||||||
| Status |
|
||||||||||
| DDM Modifiers | You may enter up to eight IDs of users; only these users will
then be allowed to maintain the DDM in Predict (or with Natural's SYSDDM
utility). If you do not specify any DDM modifier, the owners of the security
profile (see Additional
Options below) may maintain the DDM. If neither DDM modifiers nor
owners are specified, maintenance of the DDM is not restricted.
Next to the ID of each DDM modifier, you may optionally specify a number from 1 to 3; this number determines how many of the other DDM modifiers specified must countersign for maintenance permission (the countersignature logic which applies to DDM maintenance permission is analogous to that of owners and co-owners as described in the section Countersignatures). |
||||||||||
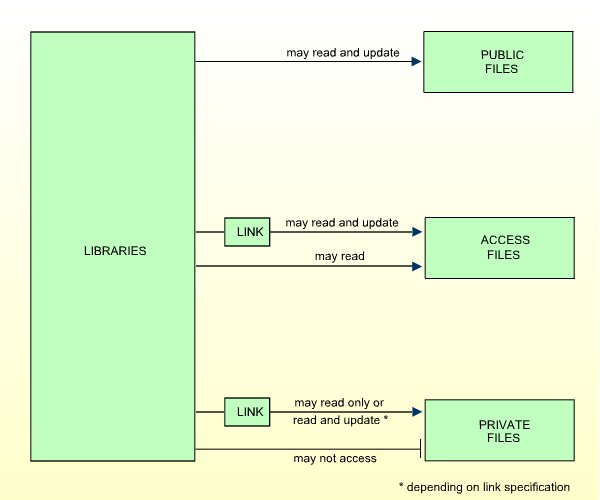
The file status of a file may be one of the following:
| PUBL | PUBLIC: The file is not protected. It may be read and updated by any library. |
|---|---|
| ACCE | ACCESS: The file is protected as far as update is concerned. It may be read by any library. However, it may be updated only by libraries that have been linked to the file. |
| PRIV | PRIVATE: The file is protected. It may be accessed only by libraries that are linked to it. A link to a PRIVATE file may be specified as "read"(that is, read only) or "update" (which implies read). |
The check whether a program may use a file is done when the program is compiled.
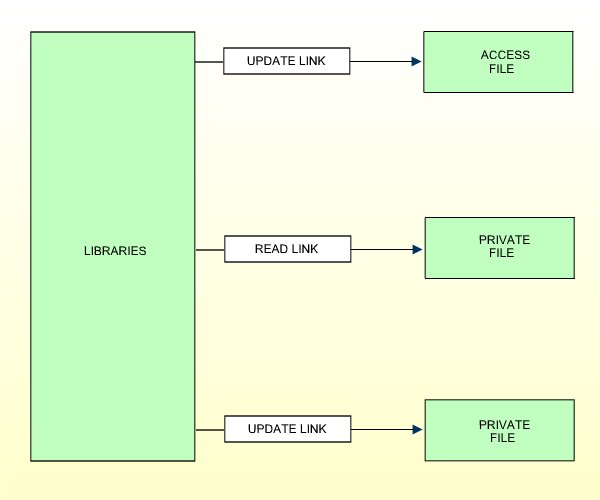
The following diagram illustrates the possible relationships between libraries and files in dependence of the file type:
To allow a library access to a file with status PRIVATE or ACCESS, a link has to be established between the library and the file. For information on how to link libraries to files, see Linking Libraries to Files below.
If you mark the field "Additional Options" on the basic security profile screen with "Y", a window will be displayed from which you can select the following options:
Maintenance Information
Security Notes
Owners
The options for which something has already been specified or defined are marked with a plus sign (+).
You can select one or more items from the window by marking them with any character. For each item selected, an additional window will be displayed:
| Additional Option | Explanation |
|---|---|
| Maintenance Information (display only) | In this window, the following information is displayed:
|
| Security Notes | In this window, you may enter your notes on the security profile. |
| Owners | In this window, you may enter up to eight IDs of
ADMINISTRATORs. Only the ADMINISTRATORs specified here will be allowed to
maintain this file security profile or link libraries to it. If no owner is
specified, any user of type ADMINISTRATOR may maintain and link the security
profile.
For each owner, the number of co-owners whose countersignatures will be required for maintenance/link permission may optionally be specified in the field after the ID. For an explanation of owners and co-owners, see the section Countersignatures . |
This section describes the functions used to create and maintain file profiles. It covers the following topics:
On the Main Menu, enter code "M" for "Maintenance". A window will be displayed.
In the window, mark the object type "File" with a character or with the cursor. The File Maintenance selection list will be displayed.
From this selection list, you invoke all file maintenance functions as described below.
When you invoke File Maintenance, a list of all files that have been defined to Natural Security will be displayed.
If you do not wish to get a list of all existing files but would like only certain files to be listed, you may use the Start Value and Type/Status options as described in the section Finding Your Way In Natural Security.
On the Main Menu, enter the code "M" for "Maintenance". A window will be displayed. In the window, mark the object type "File" with a character or with the cursor (and, if desired, type in a start value and/or file status). The File Maintenance selection list will be displayed:
12:50:20 *** Natural Security *** 2007-09-01
- File Maintenance -
Co File ID Status Message
__ ________________________________ ______ _____________________
__ ANGLOFILE PUBL
__ AUTOMOBILES PUBL
__ CLIENTES PUBL
__ DELINCUENTES PUBL
__ EMPLEADOS PUBL
__ FAHRZEUGE PRIV
__ FINANCE PUBL
__ IMPUESTOS PUBL
__ INVOICE PUBL
__ MITARBEITER PUBL
__ NAILFILE PUBL
__ NEWFILE PUBL
__ OLDFILE PUBL
__ OTRASCOSAS PUBL
__ PRO-FILE PUBL
Command ===>
Enter-PF1---PF2---PF3---PF4---PF5---PF6---PF7---PF8---PF9---PF10--PF11--PF12---
Help Exit Flip - + Canc
|
For each file, the file ID and file status are displayed.
The list can be scrolled as described in the section Finding Your Way In Natural Security.
If you wish to list only DDMs of a specific status, you can specify one of the following selection criteria in the Status field above the list:
| PUBL | All DDMs of status PUBLIC. |
|---|---|
| ACCE | All DDMs of status ACCESS. |
| RIV | All DDMs of status PRIVATE. |
| DEFI | Defined; that is, all DDMs of status PRIV, ACCE, and PUBL (*). |
| UNDF | Undefined; that is, all DDMs whose status is not PRIV, ACCE or PUBL (*). |
| DDM | All defined and undefined DDMs (*). |
| NDDM | DDM security profiles for which no corresponding DDMs exist (*). |
* This is not an actual DDM status, but for selection purposes only.
The default status for selection is "DDM"; that is, all DDMs will be listed.
The following file maintenance functions are available (possible code abbreviations are underlined):
| Code | Function |
|---|---|
AD |
Add file |
CO |
Copy file |
MO |
Modify file |
DE
|
Delete file |
DI |
Display file |
LL
|
Link libraries to file |
To invoke a specific function for a file, mark the file with the appropriate function code in column "Co".
You may select various files for various functions at the same time; that is, you can mark several files on the screen with a function code. For each file marked, the appropriate processing screen will be displayed. You may then perform for one file after another the selected functions.
This function is used to define DDMs to Natural Security, that is, create new file security profiles.
On the Main Menu, enter "M" for "Maintenance". A window will be displayed. In the window, mark object type "File" with a character and enter "UNDF" in the "Type/Status" field (and, if desired, enter a start value).
The File Maintenance selection list will be displayed, listing all files with file status "UNDEFINED" (that is, all DDMs that have been generated but not yet been defined to Natural Security).
The list can be scrolled as described in the section Finding Your Way In Natural Security.
On the File Maintenance selection list, mark the DDM for which you wish to create a file security profile with function code "AD". The Add File screen will be displayed.
The individual items you may define on this screen and any additional windows that may be part of a file security profile are described under Components of a File Profile above.
When you add a file, the owners specified in your own user security profile will automatically be copied into the file security profile you are creating.
This function is used to define a new file to Natural Security by creating a security profile which is identical to an already existing file security profile.
All components of the existing security profile will be copied into the new file security profile - except the file number and database ID (these are taken from the DDM), and the owners (these will be copied from your own user security profile into the new file security profile you are creating).
Any links existing to the existing file will not be copied.
On the File Maintenance selection list, mark the file whose security profile you wish to duplicate with function code "CO".
A window will be displayed. In this window, enter the ID of the new file.
The new security profile will be displayed.
The individual components of the security profile you may define or modify are described under Components of a File Profile above.
This function is used to change an existing file security profile.
On the File Maintenance selection list, mark the file whose security profile you wish to change with function code "MO". The security profile of the selected file will be displayed.
The individual components of the security profile you may define or modify are described under Components of a File Profile above.
This function is used to delete an existing file security profile.
On the File Maintenance selection list, mark the file you wish to delete with function code "DE". A window will be displayed.
If you have invoked the Delete File function and should then decide against deleting the given file security profile, you may leave the Delete File window by pressing ENTER without having typed in anything.
If you wish to delete the given file security profile, enter the file's ID in the window to confirm the deletion.
When you delete a file, all existing links to the file will also be deleted.
When you delete a file security profile, the DDM itself will not be deleted. The file ID will remain in the File Maintenance selection list with File Status set to "UNDEFINED".
If a DDM is uncataloged in SYSDDM, deleted with SYSMAIN, or scratched in SYSDIC (Predict), the corresponding Natural Security file profile will automatically be deleted.
If you mark more than one file with "DE", a window will appear in which you are asked whether you wish to confirm the deletion of each file security profile by entering the file's ID, or whether all files selected for deletion are to be deleted without this individual confirmation. Be careful not to delete a file accidentally.
This function is used to display an existing file security profile.
On the File Maintenance selection list, mark the file whose security profile you wish to view with function code "DI". The security profile of the selected file will be displayed.
The individual components of the security profile are described under Components of a File Profile above.
To allow a library access to a file, a link has to be established between the library and the file.
Two functions are available to establish and maintain these links:
To link one library to various files, you use the function "Link library to files" (which is invoked from the Library Maintenance selection list).
To link multiple libraries to one file, you use the function "Link libraries to file" (which is invoked from the File Maintenance selection list).
Both functions are described below. Possible link types are summarized at the end of this section.
When you invoke the function "Link Library to Files" from the Library Maintenance selection list, a list of all files with file status ACCESS and PRIVATE will be displayed. On the list you may mark the files to which you wish to link the given library.
On the Library Maintenance selection, mark the library you wish to link with function code "LF".
A window will be displayed in which you may specify a start value for the list of files. If you wish to maintain only existing links, you can select the option "Select only defined links" - in which case the list of files to be displayed will only include those files to which the library is already linked.
Then, the Link Library To Files selection list will be displayed, showing the list of files.
The list can be scrolled as described in the section Finding Your Way In Natural Security.
In the "Co" column you may mark each file with one of the following function codes (possible code abbreviations are underlined):
| Code | Function |
|---|---|
RE
|
Read-Link - The library thus linked may only read the file, but not update it. |
UP
|
Update-Link - The library thus linked may read and update the file. |
CL
|
Cancel - An existing link will be cancelled. |
DI |
Display File - The file security profile will be displayed. |
You can mark one or more files on the screen with a function code. For each file marked, the selected functions will then be executed one after another. When processing is completed, a message will be displayed stating the link situation now in effect between the library and each file.
When you invoke the function "Link Libraries to File" from the Library Maintenance selection list, a list of all libraries that have been defined to Natural Security will be displayed. On the list you may mark the libraries you wish to be linked to the given file.
On the File Maintenance selection list, mark the file to which you wish to link libraries with function code "LL".
A window will be displayed in which you may specify a start value for the list of libraries. In addition, the field "Libraries/Private Libraries" allows you to list only private libraries: if you specify "L", the list will include either all libraries including private ones (if private libraries are used in public mode) or all libraries except private ones (if private libraries are used in private mode); if you specify "U", the list will include only users' private libraries. If you wish to maintain only existing links, you can select the option "Select only defined links" - in which case the list of libraries to be displayed will only include those libraries which are already linked to the file.
Then, the Link Libraries To File selection list will be displayed, showing the list of libraries.
The list can be scrolled as described in the section Finding Your Way In Natural Security.
In the "Co" column you may mark each library with one of the following function codes (possible code abbreviations are underlined):
| Code | Function |
|---|---|
RE
|
Read-Link - The library thus linked may only read the file, but not update it. |
UP
|
Update-Link - The library thus linked may read and update the file. |
CL
|
Cancel - An existing link will be cancelled. |
DI |
Display Library - The library security profile will be displayed. |
You can mark one or more libraries on the screen with a function code. For each library marked, the selected functions will then be executed one after another. When processing is completed, a message will be displayed stating the link situation now in effect between the file and each library.
A link can only be established to a PRIVATE or ACCESS file, since there is no link required to read or update a PUBLIC file.
A link to a PRIVATE file can be specified as read-link (RE) or update-link (UP).
A link to an ACCESS file can only be specified as update-link (UP), since no link is required to read an ACCESS file.
The following figure shows all possible link types: