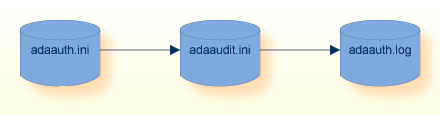
The configuration of Adabas role-based security is stored in the following files:
adaauth.ini
adaaudit.ini
These files configure the security for a local machine and apply to all databases, to all product installations and product versions that are greater than or equal to Version 6.5 on the machine.
These are ASCII files, which can be edited with a standard text editor.
The configuration file adaauth.ini is located
centrally. The location is platform-specific and is fixed; e.g. cannot be
modified. Initially, the files adaaudit.ini and
adarbac.ini are also located in the predefined location. These
files can be moved as required to other locations.
| File | Description | Fixed Location |
|---|---|---|
adaauth.ini |
Configuration Definitions | Yes |
adaaudit.ini |
Audit Log Configuration | No |
adaaudt.log |
Audit Log | No |
adarbac.ini |
DEPRECATED | N/A |
Note:
It is mandatory that all users who are authorized to execute an
Adabas utility, have READ/WRITE access permissions to both the log file and the
directory in which it is located.
The configuration and audit log files are installed into the following locations:
%PROGRAMDATA%\Software AG\Adabas\auth
adaauth.ini
adarbac.ini
adaaudit.ini
%PROGRAMDATA%\Software AG\Adabas\log
adaaudit.log
The configuration and audit log files are installed into the following locations:
/etc/softwareag/Adabas/auth
adaauth.ini
adarbac.ini
adaaudit.ini
/var/log/softwareag/Adabas
adaaudit.log
Important:
The configuration and audit log files mentioned above are
installed without restrictive file permissions. Please refer to
Security
Considerations in the Adabas Security
Facilities documentation, for further details on how to secure
(“harden”) the dataset.
All users of Adabas utilities require the following minimal file and directory permissions:
READ privileges to the configuration files.
WRITE privileges to the Audit Log File (LOG_FILE setting)
WRITE privileges to the directory in which the Audit Log File is located.
The configuration file adaauth.ini contains information
which applies to the machine and to all databases, to all product installations
and product versions that are greater than or equal to Version 6.5 on the
machine.
This file contains the following basic security definitions:
The location of the security configuration definitions.
The location of the audit configuration file.
The configuration file adaauth.ini contains a single
section with the topic AUTHZ.
The section starts with a line containing the name of the topic
enclosed in square brackets, using the syntax
[topic-name]. The topics relevant to
security definitions are:
AUTHZ, with items
ACTION
AUDIT_FILE
MODE
RBAC_FILE
The topic AUTHZ contains information used to configure security for the local machine.
The syntax for the topic AUTHZ is as follows:
[AUTHZ] ACTION = <activation of feature> MODE = <source of definitions> AUDIT_FILE = <path to adaaudit.ini> RBAC_FILE = <DEPRECATED> [AUTHZ-END]
The item ACTION activates the Adabas role-based security feature.
YES
enables the feature.
NO
disables the feature.
The default setting is YES.
Important:
The item ACTION will be depreciated in a future
release.
The item MODE defines the source of the security definitions.
ADABAS
The security definitions are defined in the RBAC system
file.
INI
This setting is deprecated.
The item AUDIT_FILE defines the location of the file
adaaudit.ini, which contains the configuration of the audit
processing; e.g. the layout and location of the audit log.
Usage of the item RBAC_FILE is DEPRECATED..
The configuration file adaaudit.ini contains
information which applies to the machine and to all databases, to all product
installations and product versions that are greater than or equal to Version
6.5 on the machine.
This file contains the following information:
Basic configuration audit file processing; e.g. the layout and location of the audit log.
The configuration file adaaudit.ini contains a single
section with the topic AUDIT.
The section starts with a line containing the name of the topic
enclosed in square brackets, using the syntax
[topic-name]. The topics relevant to
security definitions are:
AUDIT, with items
FORMAT
LOG_FILE
SEPARATOR
The topic AUDIT defines the parameters of the Audit Log.
The syntax for the topic AUDIT is as follows:
[AUDIT] FORMAT = <file layout> SEPARATOR = <token separator> LOG_FILE = <log file name> [AUDIT-END]
The item FORMAT defines the layout of an audit log entry.
TEXT
All values in the audit entry are preceded by a header and
separated by blanks.
CSV
All values in the audit entry are separated by the separator
value.
The item SEPARATOR defines the character to be used to separate values in CSV format.
Valid parameter values for SEPARATOR are:
| Parameter Value | Description |
|---|---|
"," |
Comma |
";" |
Semi-Colon |
"/t" |
Tabulator |
" "
|
Blank (Default) |
The parameter value must be quoted.
Note:
The parameter value for Tabulator is the string
"/t".
The item LOG_FILE defines the location and file name of the audit log.
Important:
The content and usage of the configuration file
adarbac.ini is DEPRECATED.
The following steps describe how to enable and use the feature Authorization for Adabas Utilities:
Set MODE=ADABAS in the configuration file
adaauth.ini.
Enable the feature Authorization for Adabas Utilities.
Use ADARBA to define site-specific security definitions.